Human Risk Management: Your First Line of Cyber Defence
Why employees are the most targeted attack surface, and how businesses can turn human risk into human resilience

Why Human Risk Management Is the Missing Layer in Your Cybersecurity Strategy
When businesses think about cybersecurity, they often picture firewalls, endpoint protection, and monitoring tools. But one of the most significant risks doesn’t sit in your tech stack, it sits with your people.
Human risk management focuses on understanding, measuring, and reducing the likelihood of employees making security mistakes. And in today’s threat landscape, that’s not optional, it’s critical.
Most cyberattacks don’t start with sophisticated hacking. They start with simple human actions:
- Clicking a phishing link
- Reusing weak passwords
- Mishandling sensitive data
These aren’t failures of intelligence, they’re failures of awareness, process and environment.
Why it matters more than ever
Attackers have evolved. Instead of breaking through systems, they log in through people. Social engineering tactics are now highly targeted, convincing and often indistinguishable from legitimate communication.
Without a human risk strategy, businesses face:
- Increased likelihood of breaches
- Higher financial and reputational damage
- Compliance and regulatory exposure
And importantly, traditional “tick-box” training isn’t enough anymore.
What effective human risk management looks like
It’s not about blaming employees, it’s about designing a system that supports better decisions.
A strong approach includes:
- Continuous, scenario-based training (not annual videos)
- Phishing simulations that reflect real-world attacks
- Behavioural insights to identify high-risk users
- Clear reporting processes for suspicious activity
The goal is to shift from awareness to behaviour change.
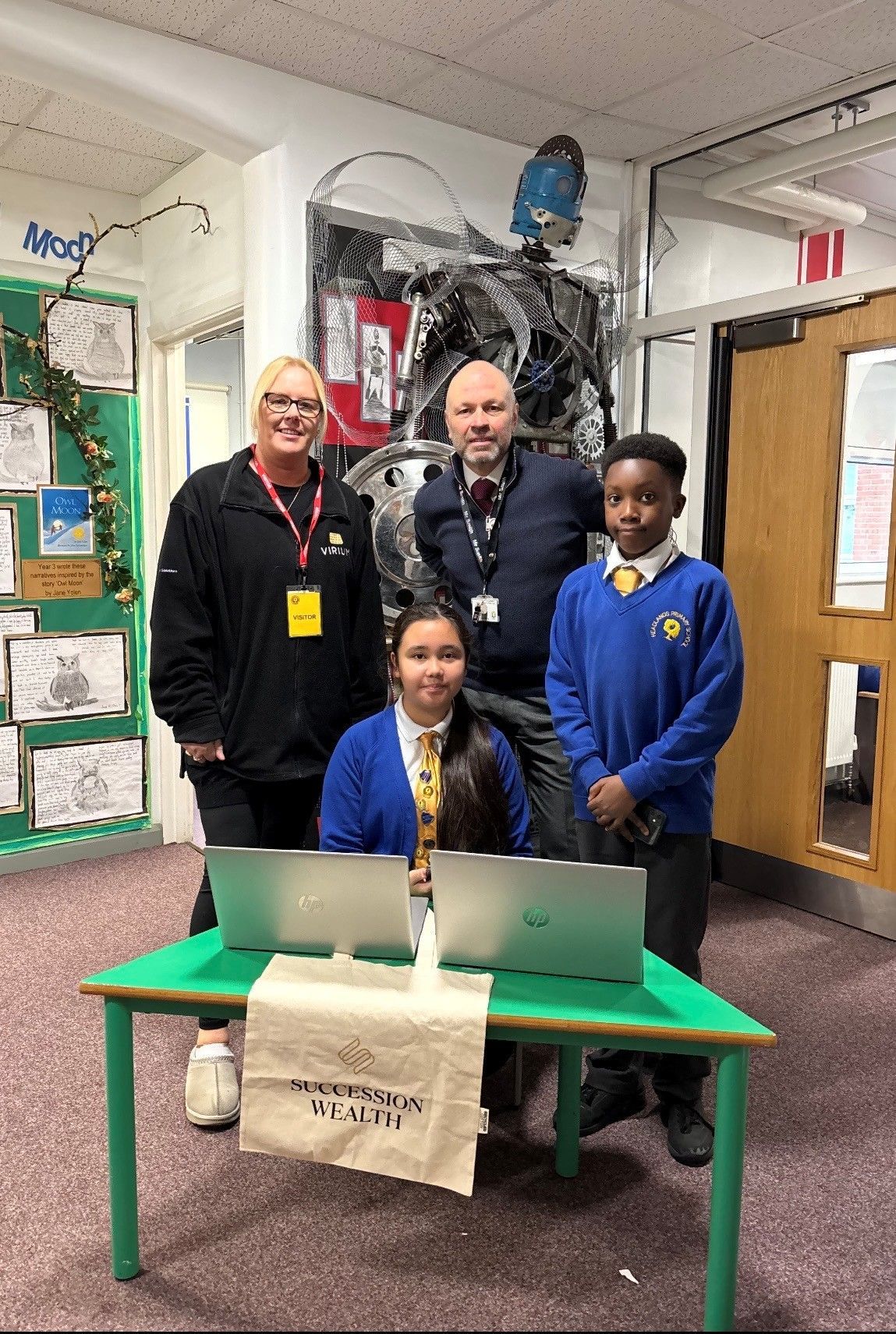
The business impact
Organisations that invest in human risk management don’t just reduce incidents, they build resilience. Employees become an active line of defence rather than a vulnerability.
Over time, this leads to:
- Fewer successful attacks
- Faster incident response
- A stronger security culture across the business
In a world where attackers target people first, your security strategy should too.